BLOG
- June 11, 2019
On the 14th of January 2020 Microsoft will implement four major end of support, otherwise known as “end of life”...
- June 4, 2019
A recent survey found that 88% of IT professionals considered endpoint management an essential part of technology strategy, while almost...
- May 2, 2019
Every year, 60% of small businesses suffer from cyberattacks, putting pressure on IT service providers, enterprises, and governments to raise...
- April 23, 2019
For small businesses, a holistic software solution that is capable of handling a multitude of tasks simultaneously saves precious time...
- March 4, 2019
A good indicator of business growth is expansion to new locations, and with it comes the need to consolidate operations....
- January 16, 2019
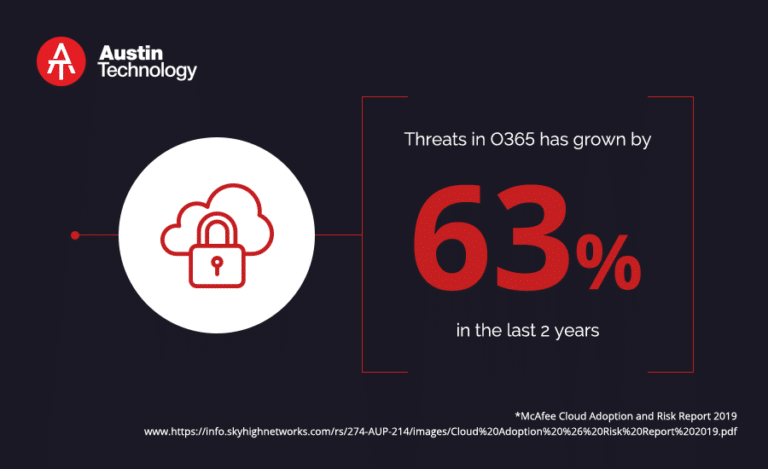
Over a million companies around the world are now using Microsoft Office 365, the world’s industry standard in workplace productivity...
- January 9, 2019
As businesses migrate to the cloud and make use of an ever-wider range of web and mobile technologies, cyberattacks are...
- October 14, 2018
Spam emails are an unsolicited chain of emails sent in bulk. They were used in the past for some good-hearted...
- September 25, 2018
Cloud computing is a must-have solution for cutting costs and increasing productivity. But it may be difficult to achieve these...
- August 17, 2018
Outsourced IT providers love to rattle off statistics when trying to convince owners of small- and medium-sized businesses (SMBs) how...